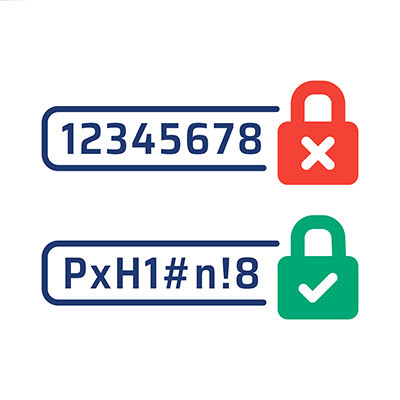
You’ve probably heard a lot of password advice over the past decade, but how much of it is actually good advice that you should listen to? These days, with advanced automated threats able to crack incredibly complex passwords with ease, you can’t be too careful. You might even need to take a different approach entirely… which brings us to the OG password advice: just make it longer.
Heart of Texas Network Consultants Blog
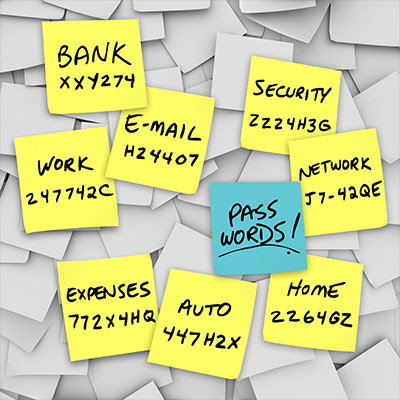
How many employees do you have who keep your company’s passwords on sticky notes stuck to their monitors? This simple, seemingly benign trick could be putting your business at risk. After all, if you can see the password on a sticky note, so too can others who happen to be wandering around the office—including potential threat actors.
It would seem that the people responsible for the recent heist at the Louvre, which netted over $101 million in jewelry, may have used a more complicated plan than strictly necessary. According to a French publication, the famous museum has a long history of cybersecurity mistakes and faux pas… many of which, given the museum’s fame, are truly shocking.
Let’s go over what we know about the Louvre’s protections over the years, and what they suggest about the current state of things. We’ll probably learn a thing or two by doing so.
It’s easy for employees to reuse passwords just to make things easier for themselves; after all, why use different passwords when you have a dozen accounts to remember passwords for? Unfortunately, this habit will come back to bite you, especially if your business is ever involved in a data breach. These credentials could be put up for sale on the dark web… and that’s just the beginning of your problems.
While still critical to get right, passwords aren’t nearly as secure as you would expect them to be. They can be guessed (especially if proper password practices haven’t been followed), stolen in data breaches, or phished from a well-meaning—albeit shortsighted—employee.
Passwords are basically the lock built into the front door of a building. They’re enough to keep out honest people, but what about the people who are willing to go to the deep web and 3D print the master key to the type of lock you use?
A successful business is a secure business. You probably have a good lock on the front door, maybe an alarm system, and secure cabinets for important documents. You do all of this to protect your business' physical assets from threats. So why wouldn't you do the same for your digital assets?
Just as you have physical security measures, your business also needs strong cybersecurity policies. They help create clear rules for employees to follow and a plan to fall back on if an incident occurs.
Tips are great as long as they actually work. Business owners need more technology tips than just about anything else, whether that is app-specific or general care of technology. We try to do our best to provide useful tips a couple of times a month, but this week we wanted to focus on what is probably the most important tip we can provide.
Fairly recently, news circulated that a data breach had exposed 16 billion—yes, with a “b”—passwords for various logins, including social media accounts, virtual private networks, corporate tools, and more. Effectively, every online service imaginable was represented in this breach.
This is very bad… arguably unprecedented.
However, this impression is at best misleading. Let’s dig into the truth of the matter, while still acknowledging that there are some lessons to be learned.
Running a business is already confusing enough without worrying about security at all times. Whether you’re a small business owner or a multi-level enterprise, security is just as important for all the same reasons. Today, we want to share a couple of security strategies you can implement today to feel better about the current state of your infrastructure moving forward.
The Disney brand has long cultivated an image of magic and wonder. However, this image has yet to materialize any magical effects in reality. For example, people still suffer from food allergies while visiting Disney’s various parks.
This makes it especially dangerous that a former Disney employee was allegedly still able to access a specialized menu-planning app and make alterations, like changing prices, adding language that Disney certainly would not approve of, switching text to the unintelligible “Wingdings” font, and worst of all… changing menu information.
Passwords have long been one of the central pillars of account security on the Internet. Combined with a username, they make up the foundation of most login systems. Because of this, they are a hot commodity for hackers who want to steal credentials and infiltrate accounts or networks. In recent years, however, other security measures have exposed the weakness of poor passwords for security, leading to the adoption of other measures.
It doesn’t matter who you are; your age, your occupation, your employment status, your station in life—you need to make 2024 the year you get your cybersecurity hygiene in check. What we’re going to talk about today isn’t overkill, overly complicated, or expensive. This isn’t us trying to sell you on something. In fact, this is probably the easiest New Year's Resolution you can give yourself.
First, let me start with a really quick story.
One of the reasons that information technology keeps changing is for the sake of the user and their convenience using it. However, if this convenience comes at the sacrifice of your business’ cybersecurity, it just isn’t worth it. This is the crux of why we always recommend that any organization seeking to use password management should invest in a reputable password management software, rather than the built-in capabilities of modern browsers.
Whether you love them or hate them, passwords serve an important purpose in the realm of cybersecurity. They are the first line of defense against potential threats, yet they are also notoriously easy to crack. Some of the biggest names in technology have been working on ways to get around the challenges presented by password security, including one that we are excited to highlight in today’s blog.
Simple passwords are often the bane of a business’ existence. If you routinely use strings like Password, 123456, Guest, or Qwerty to secure an account, then you need to reexamine your password practices before they lead to a data breach. A good password can go a long way toward helping you in this effort.
User authentication is a critical security feature for a business, specifically because it helps to minimize a significant threat to your business. This is why we’re so adamant that you should require multi-factor authentication wherever it is available… but is a better way to authenticate your users on the horizon?
Passwords have been a primary data security measure since 1960, when MIT researcher Fernando Corbató suggested the practice—although even he is reportedly slow to take full credit. Why? Well, if you ask Corbató (and his contemporaries, who were the first to implement passwords as we’d recognize them today), the security concerns were limited.
So, have we reached the point where it would be best to replace passwords as the default authentication measure?
Most accounts these days require a password of some sort, and as such, the average user has countless of these codes that need to be kept both secure and top-of-mind. Some web browsers have built-in password management tools to help make them more user-friendly, but with so much convenience involved, one has to ask whether or not these built-in management tools are as secure as they should be.
If I were to tell you that one variable was responsible for more than 80 percent of cyberattacks, what would you guess that variable was? If you guessed “stolen access credentials,” you’d be correct. The traditional username/password combination may soon be a thing of the past as more tech companies transition to alternative authentication measures.